Active Directory / LDAP for staff
Overview
Active Directory / LDAP for staff is additional authentication plugin you can add to your HostBill. It allows your staff to authenticate in HostBill using their Active Directory / LDAP credentials.
Activating the module
- If the plugin is included in your HostBill edition you can download it from your client portal.
- If the plugin is not included in your HostBill edition you can purchase it from our marketplace and then download it from the client area.
- Once you download the plugin extract it in the main HostBill directory.
- Go to Settings → Modules, find and activate Auth_LDAP plugin.
- Once the plugin is activated you will be directed to Settings→ Modules→ Plugins to configure LDAP authentication.
Note
Module requires php-ldap extension to be installed in system to function properly
Module confiuration
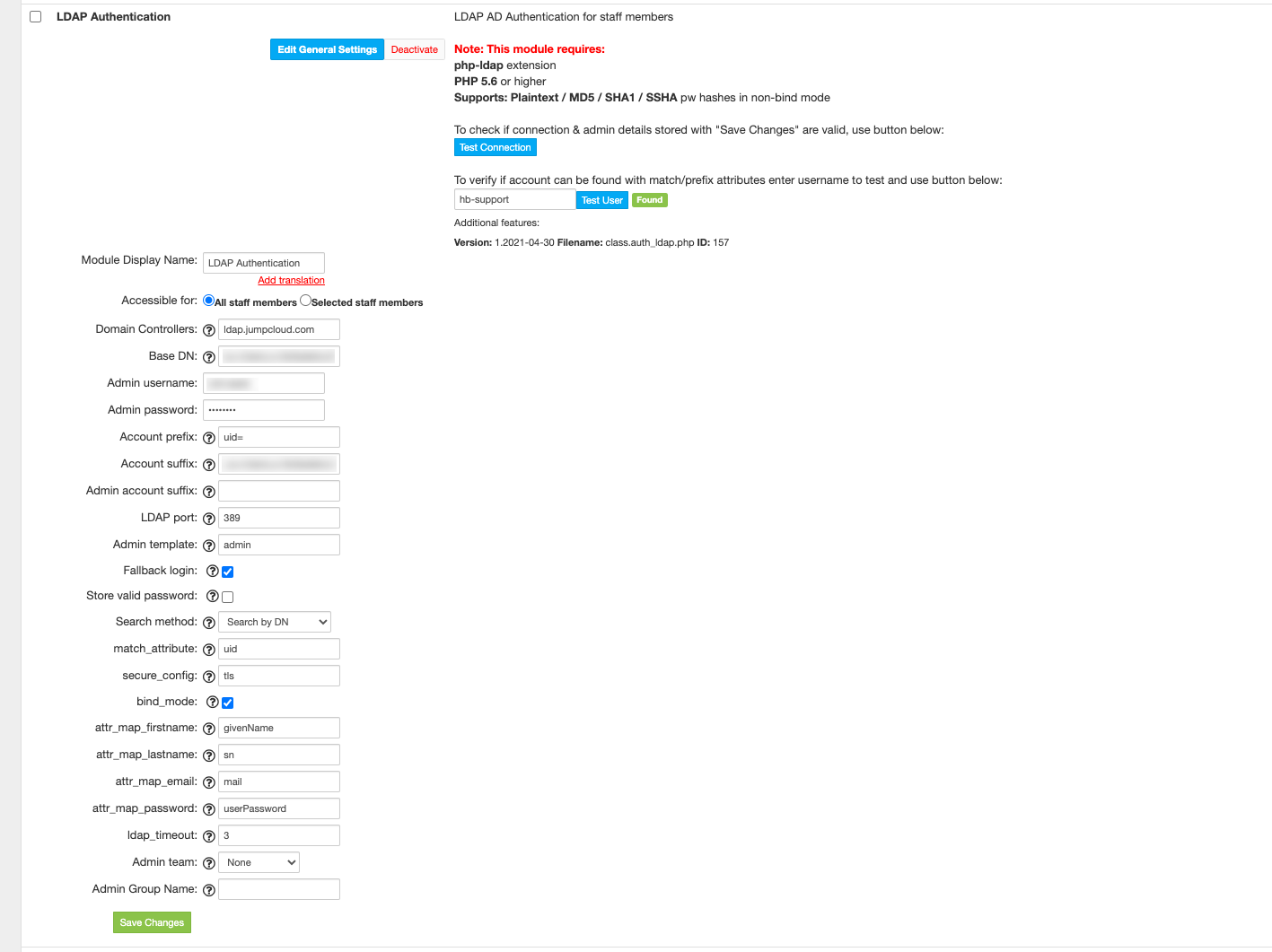
For the AD/LDAP module the following configuration options are available:
Domain Controllers: Enter your AD server hostname or list of hostnames separated with a comma
Base DN: Enter your Base DN, for example: OU=Base,DC=acme,DC=org
Admin username: Your LDAP/AD admin username used to search for users/connecting with domain controller
Admin password: Your LDAP/AD admin password for above username
Account prefix: If all accounts in your LDAP/AD are prefixed with some string, for ease of use you can prefix them here. When logging in your staff will not be required to enter this prefix
Account suffix: If all accounts when login are required to enter suffix (ie. login with admin@acme.org), you can enter it here, so staff will not need to enter it (ie. login only with "admin")
Admin account suffix: If your admin account username specified in setting above needs to be suffixed, you can also enter it here
LDAP port: enter your LDAP server port, default: 389
Admin template: When your staff log in into HostBill using LDAP, and they do not have related account in HostBill, this module will create it for them. Here you can enter username of staff that is already in HostBill as a template for privileges set.
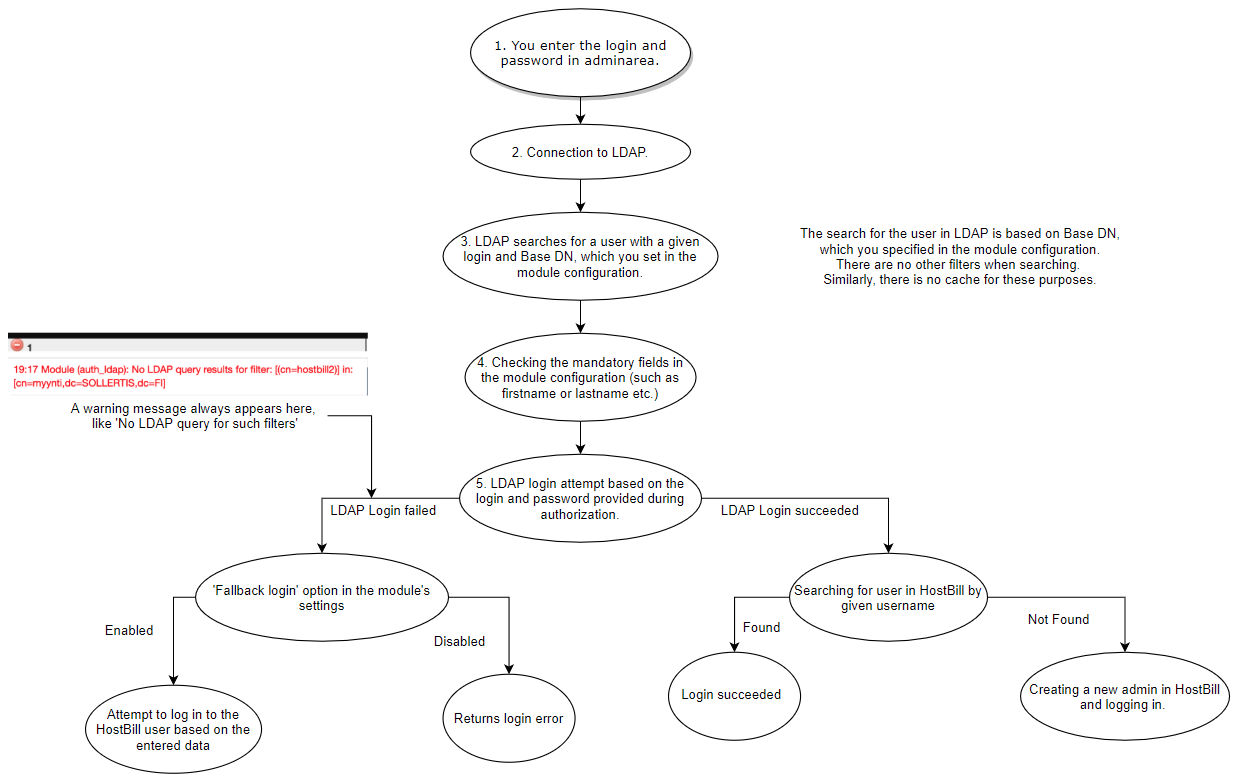
Fallback login: When enabled, if LDAP server does not work or user is not found in LDAP, HostBill database will be used as a fallback login.
Warning: Without this option enabled, if LDAP is not responding you can be locked out of your admin area.Store valid password: When fallback login is enabled, once staff login their valid password that authenticates against LDAP can be stored in HostBill database for future logins.
- Search method: select from available methods:
- Search by attribute - with this (default) enabled option module will attempt to find entered username by attribute specified in match_attribute setting
- Search by DN - with this option enabled module will attempt to find user by full DN built out of <account prefix>username<account suffix>
- match_attribute - used when search method is set to "search by attribute", ie cn, or userprincipalname
- secure_config - secure connection method to AD/LDAP. Either ssl or tls or blank. Make sure OpenLDAP tools (i.e: ldapsearch) are capable of querying your secured LDAP server before enabling.
- bind_mode - When enabled, the module tries to bind to the ldap server using user credentials. When off, the hash function is used. Enable for ActiveDirectory logins
- attr_map_firstname - LDAP Attribute containing user's first name, i.e: givenname
- attr_map_lastname - LDAP Attribute containing user's last name, i.e: sn
- attr_map_email - LDAP Attribute containing user's email, i.e: mail
- attr_map_password - with bind mode disabled this attribute will be used to attempt to match user password.
- ldap_timeout - Ldap connection timeout (in seconds)
- Admin team - Select admin team (or none) from your HostBill that newly created staff member not present in HostBill will be auto-assigned to
- Admin Group Name - If direct search of user by attribute or DN fails in LDAP, module can perform failback search in group members. Enter group name to search in
Note
After saving changes you can use Test Connection option to check if HostBill can connect/login to domain controller using admin user/password specified.
After confirming you can connect you can also use "Test user" feature in module description to verify whether module can find user entered in test field using current module settings, without the need of re-login
Recovering default login method on lockout
Once module is enabled and no fallback login method is enabled, you may not be able to login in case ldap connection fails for some reason.
To revert to default authentication method you need to disable module in database directly. In order to do so perform following sql query against your HostBill database:
UPDATE hb_modules_configuration SET active = 0 WHERE filename = 'class.auth_ldap.php';