Overview
...
Overview
...
IP2Location is a provider of IP geolocation technology and database products, widely used in securing, enhancing and customizing Internet experience. IP2Proxy Proxy Detection Database contains IP addresses which are used as VPN anonymizers, open proxies, web proxies and Tor exits, data center, web hosting (DCH) range, search engine robots (SES) and residential proxies (RES). Anonymous proxy servers are intermediate servers meant to hide the real identity or IP address of the requestor and are often used for online credit card fraud and spamming. With IP2Proxy integration you can check customer order for potential Proxy use and reject orders from selected types of proxies, countries, certain ISP types or IP2Proxy threats detected. The verification can be omitted for admin orders.
Activating the module
...
The plugin is free and available to all HostBill users. In order to activate the plugin go to to Settings→ Modules→ Plugins → Inactive, find and activate activate IP2Proxy plugin plugin.
- Once the plugin is activated you will be directed to to Settings→ Modules→ Plugins Plugins to configure the module.
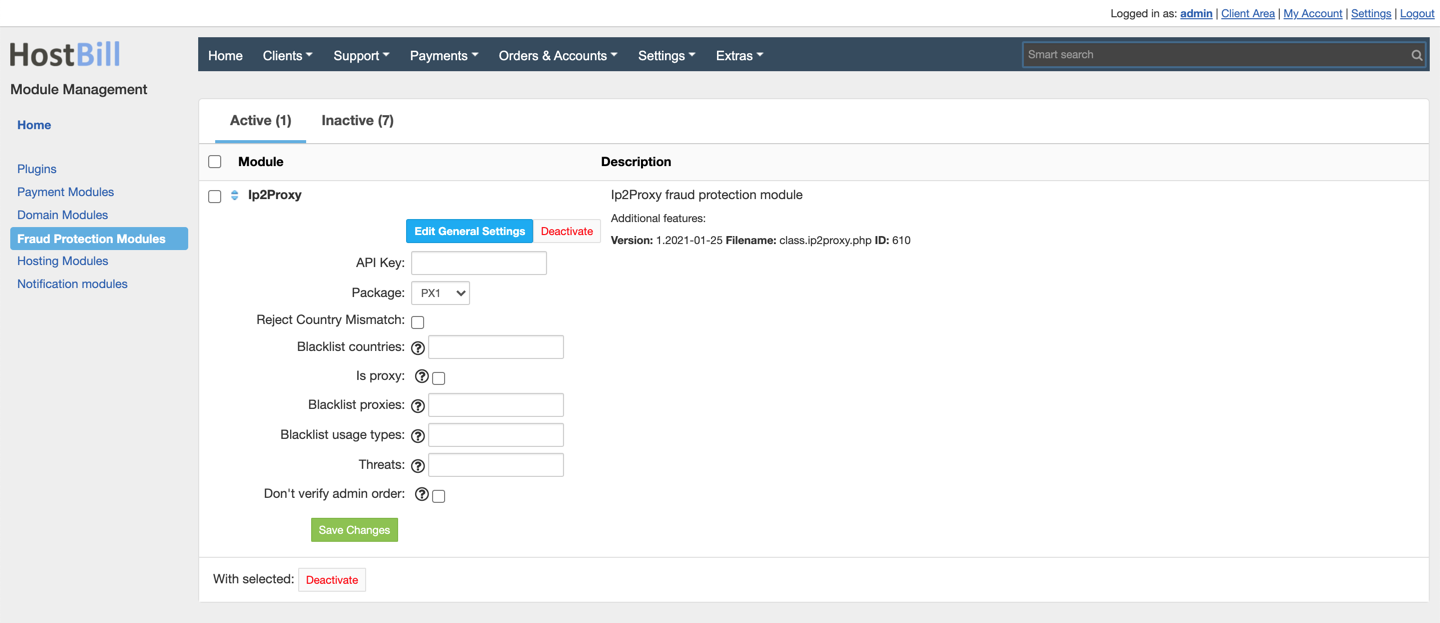
Module configuration
...
Fill in the configuration fields:
- API Key - Provide API key for IP2Proxy Web Service
- Package - Select IP2Proxy package/detection level, note that features/detections are package-specific
- Reject Country Missmatch - when enabled and customer-entered country differs from IP-detected country order will be rejected
- Blacklist Countries - enter a comma-separated list of countries detected by IP address to reject order from
- Is proxy - when enabled and any type of proxy use is detected order will be rejected
- Blacklist proxies - enter comma-separated list of proxy types (actual list available at IP2proxy website) to reject orders from
- Blacklist usage types - enter comma-separated list of usage type classification codes (ISP or company) to reject orders from (actual list available at IP2proxy website)
- Threats - enter comma-separated list of detected threats to reject orders from